The Bug Bounty Blueprint (2026): A Step-by-Step Manual Guide to Finding High-Value Vulnerabilities & Earning Bigger Rewards
Want to earn real money from bug bounties — not just low-paying reports?
This practical, manual-focused blueprint teaches you how to approach bug bounty hunting strategically, analyze applications deeply, and identify high-impact vulnerabilities that lead to serious payouts.
Instead of relying only on automated scanners, you’ll learn how elite hunters think, scope targets correctly, and manually uncover weaknesses others miss.
This guide focuses on:
- Strategy
- Reconnaissance
- Deep manual analysis
- Impact evaluation
- Reward optimization
🚀 What You’ll Learn Inside
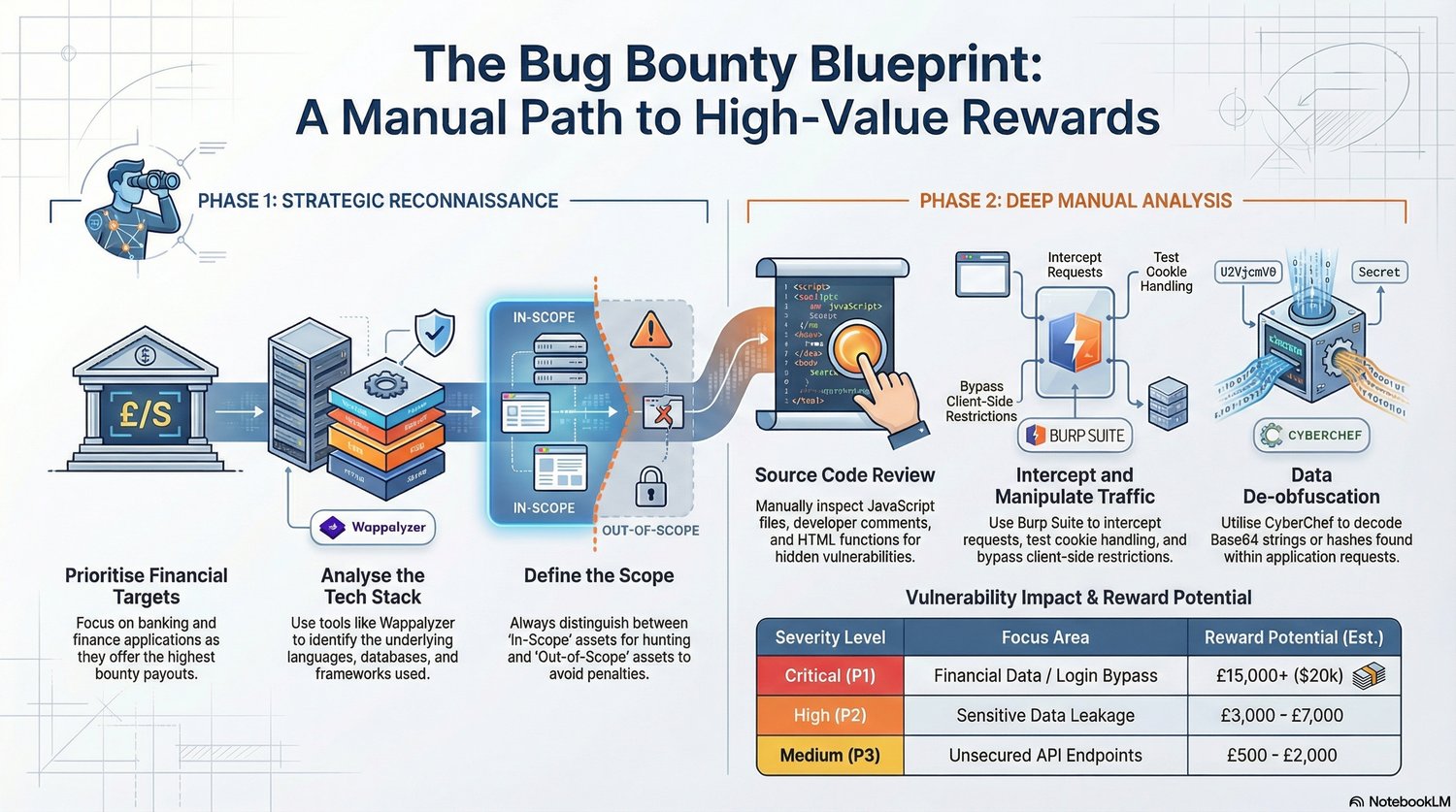
🕵️ Phase 1: Strategic Reconnaissance
- How to prioritize high-paying financial targets
- Identifying tech stacks using tools like Wappalyzer
- Understanding frameworks, databases, and backend structures
- Properly defining in-scope vs out-of-scope assets
- Avoiding costly mistakes and program penalties
🔍 Phase 2: Deep Manual Analysis
- Manual JavaScript and source code review
- How to inspect hidden endpoints and comments
- Intercepting and analyzing traffic using Burp Suite
- Testing cookie handling and session behavior
- Understanding client-side restrictions and logic flows
- Basic concepts behind decoding and data inspection
💰 Vulnerability Prioritization Strategy
Learn how to focus on higher impact areas such as:
- Authentication flows
- Financial data exposure
- Sensitive API endpoints
- Login and session handling logic
Understand how impact levels influence reward potential and how to write reports that increase acceptance chances.
🎯 Who This Guide Is For
✔ Beginners entering bug bounty
✔ Developers moving into security testing
✔ Cybersecurity students
✔ Freelancers wanting side income
✔ Manual testing enthusiasts
✔ Anyone serious about ethical hacking
🔥 What Makes This Different
This is not a generic “install a scanner” guide.
This blueprint emphasizes:
- Thinking like a security analyst
- Manual inspection skills
- Strategic target selection
- High-value vulnerability focus
- Structured hunting methodology