Bug Bounty Blueprint: Complete Ethical Hacking Guide from Reconnaissance to High-Paying Vulnerabilities
Want to learn how successful bug bounty hunters discover vulnerabilities and earn rewards from real companies?
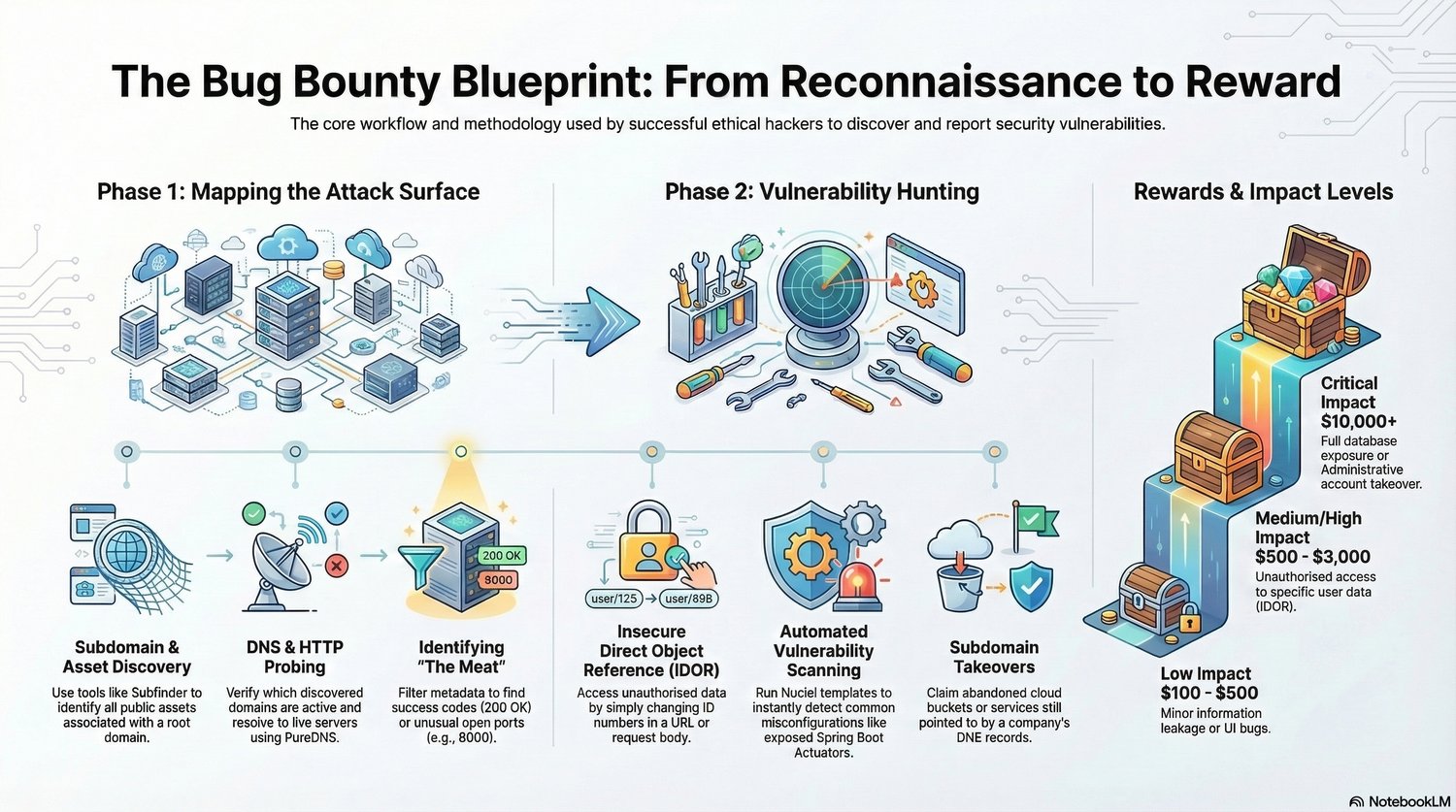
The Bug Bounty Blueprint: From Reconnaissance to Reward is a practical guide that explains the complete workflow used by ethical hackers to identify, analyze, and responsibly report security vulnerabilities.
Instead of random hacking techniques, this guide focuses on a structured methodology used in real bug bounty programs — from mapping the attack surface to discovering high-impact vulnerabilities.
Inside this guide, you’ll learn:
✔ How to map a target’s attack surface and digital assets
✔ Subdomain and asset discovery techniques used by bug bounty hunters
✔ DNS and HTTP probing to identify active services
✔ How to filter large datasets to find valuable attack targets
✔ Understanding vulnerabilities like IDOR (Insecure Direct Object Reference)
✔ Automated vulnerability scanning using tools like Nuclei
✔ Detecting cloud misconfigurations and subdomain takeovers
✔ How bug bounty reward tiers work (low, medium, and critical impact)
This guide is perfect for:
• Beginner bug bounty hunters
• Ethical hackers learning vulnerability discovery
• Cybersecurity students studying penetration testing
• Developers interested in application security
• Security researchers building structured workflows
By following this blueprint, you’ll understand how to systematically find vulnerabilities instead of relying on guesswork.
Learn the methodology used by professional bug bounty hunters and start discovering real security issues.