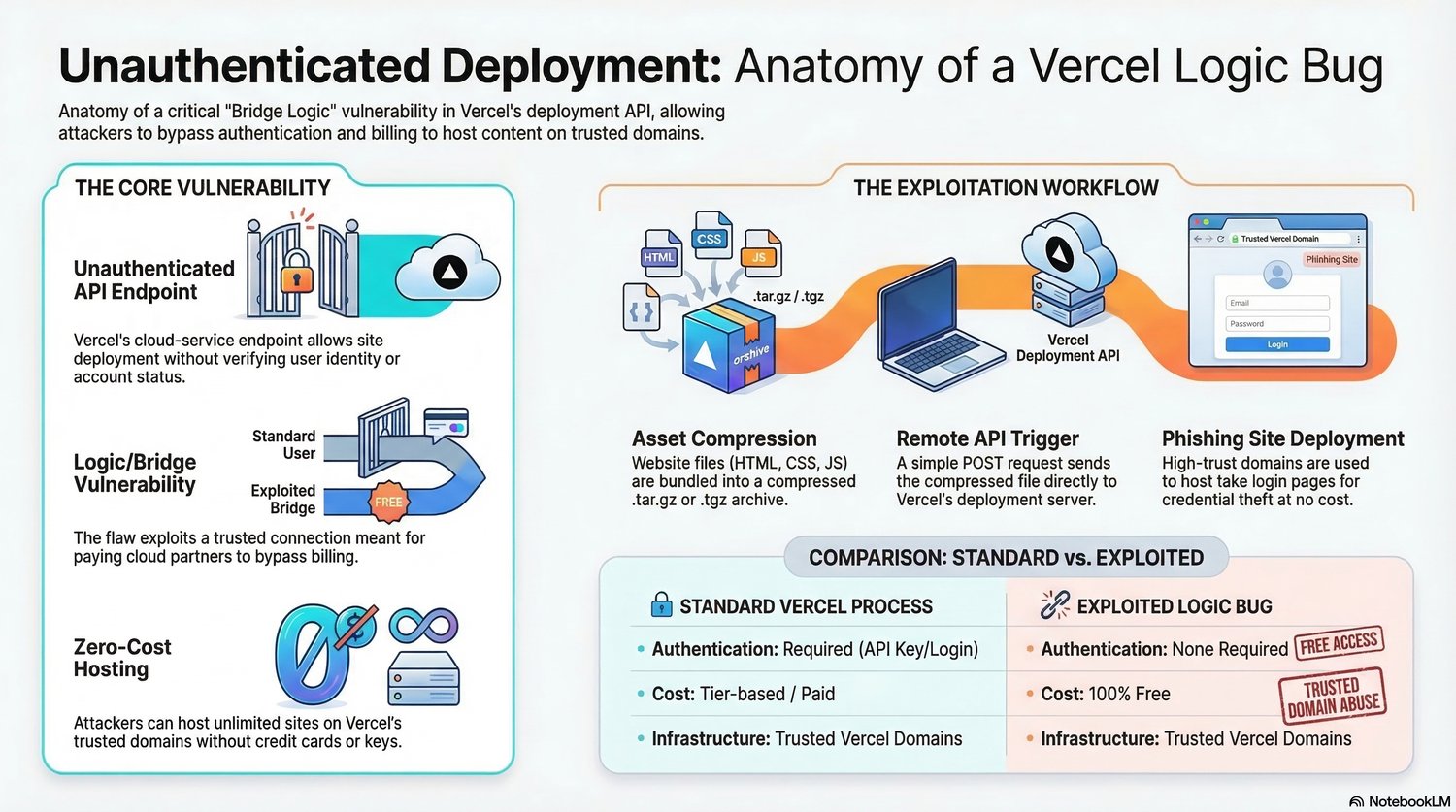
Unauthenticated Deployment: Anatomy of a Vercel Logic Bug – Cloud Security, Auth Bypass & Bug Bounty Case Study
Want to understand how a logic flaw in a cloud deployment workflow can lead to authentication bypass, zero-cost hosting abuse, and high-trust phishing infrastructure?
Unauthenticated Deployment: Anatomy of a Vercel Logic Bug is an advanced cybersecurity case study that breaks down the anatomy of a critical logic/bridge vulnerability in a cloud deployment pipeline.
This guide is designed for bug bounty hunters, ethical hackers, web security researchers, and cloud security learners who want to understand how real-world logic bugs work beyond simple XSS or IDOR findings.
Instead of focusing on basic vulnerabilities, this guide explores a more advanced class of issue: authentication bypass through flawed deployment logic, where a trusted infrastructure pathway can be abused to host malicious content on legitimate domains.
Inside this guide, you’ll learn:
✔ How an unauthenticated API endpoint can become a critical security risk
✔ The concept of a logic/bridge vulnerability in modern cloud deployment systems
✔ How trusted infrastructure relationships can be abused to bypass authentication and billing controls
✔ Why zero-cost hosting on trusted domains creates high-impact phishing and abuse scenarios
✔ A step-by-step breakdown of the exploitation workflow, including:
- Asset compression
- Remote API trigger
- Deployment pipeline abuse
- Trusted domain phishing deployment
✔ The difference between a standard deployment flow and an exploited logic bug flow
✔ Why cloud platform trust assumptions can create dangerous security blind spots
✔ How logic flaws differ from traditional vulnerability classes like XSS or SQL injection
✔ Why this type of issue is highly relevant in bug bounty and cloud security research
✔ How to think about business impact, trust abuse, and real-world exploitation paths
This guide is perfect for:
- Bug bounty hunters
- Ethical hackers
- Web application security researchers
- Cloud security learners
- Advanced cybersecurity students
- People interested in logic bugs and auth bypasses
- Researchers studying deployment pipeline abuse
- Anyone looking for a real-world cloud security case study
If you want to go beyond beginner vulnerabilities and understand how modern logic bugs in cloud systems can lead to serious security impact, this guide offers a clear and practical breakdown of a high-value vulnerability class.
Study real-world logic flaws. Understand cloud trust abuse. Think like a higher-level bug bounty hunter.