XSS Unmasked: Complete Cross-Site Scripting (XSS) Guide for Ethical Hackers & OWASP Top 10 Security
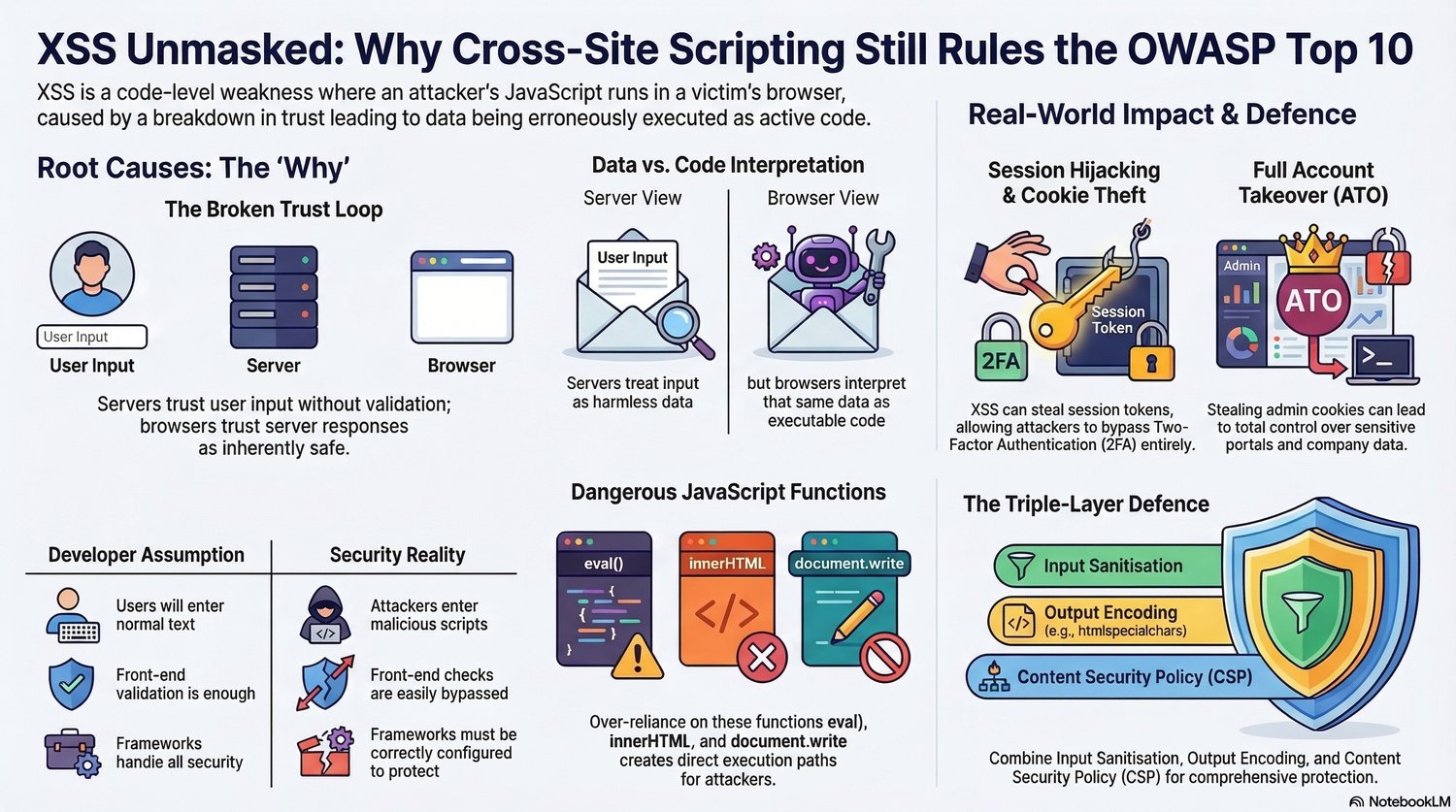
Cross-Site Scripting (XSS) remains one of the most dangerous and widely exploited vulnerabilities in modern web applications, consistently appearing in the OWASP Top 10 security risks.
XSS Unmasked: Why Cross-Site Scripting Still Rules the OWASP Top 10 is a practical cybersecurity guide that explains how XSS vulnerabilities work, why they occur, and how developers and ethical hackers can detect and prevent them.
This guide breaks down the technical concepts behind XSS attacks in a clear, visual way so both security researchers and developers can understand the risks and implement proper defenses.
Inside this guide, you’ll learn:
✔ What Cross-Site Scripting (XSS) is and how it works
✔ The root cause of XSS vulnerabilities in modern web applications
✔ How browsers interpret malicious JavaScript code from user input
✔ Real-world attack impacts such as session hijacking and cookie theft
✔ How attackers can perform full account takeover (ATO) through XSS exploits
✔ Dangerous JavaScript functions like eval(), innerHTML, and document.write
✔ Common developer misconceptions that lead to security flaws
✔ The triple-layer defense strategy: Input Sanitization, Output Encoding, and Content Security Policy (CSP)
This guide is perfect for:
• Ethical hackers and bug bounty hunters
• Web developers learning secure coding practices
• Cybersecurity students studying OWASP vulnerabilities
• Penetration testers analyzing web application security
• Anyone interested in modern web security threats
By understanding how XSS vulnerabilities work, you’ll be able to identify security flaws, protect web applications, and improve your cybersecurity knowledge.
Learn how attackers exploit XSS—and how to stop them.