No-Code Bug Bounty Automation: Build Ethical Hacking Workflows with n8n, AI & Security APIs
What if you could automate bug bounty reconnaissance, vulnerability monitoring, and security research — without writing complex code?
No-Code Hacking: Automating Bug Bounties with n8n is a practical guide that shows ethical hackers how to build powerful security automation workflows using n8n, APIs, and AI tools.
Instead of manually monitoring programs, scanning assets, and filtering vulnerabilities, this guide teaches you how to create automated pipelines that work 24/7.
Inside this guide, you’ll learn:
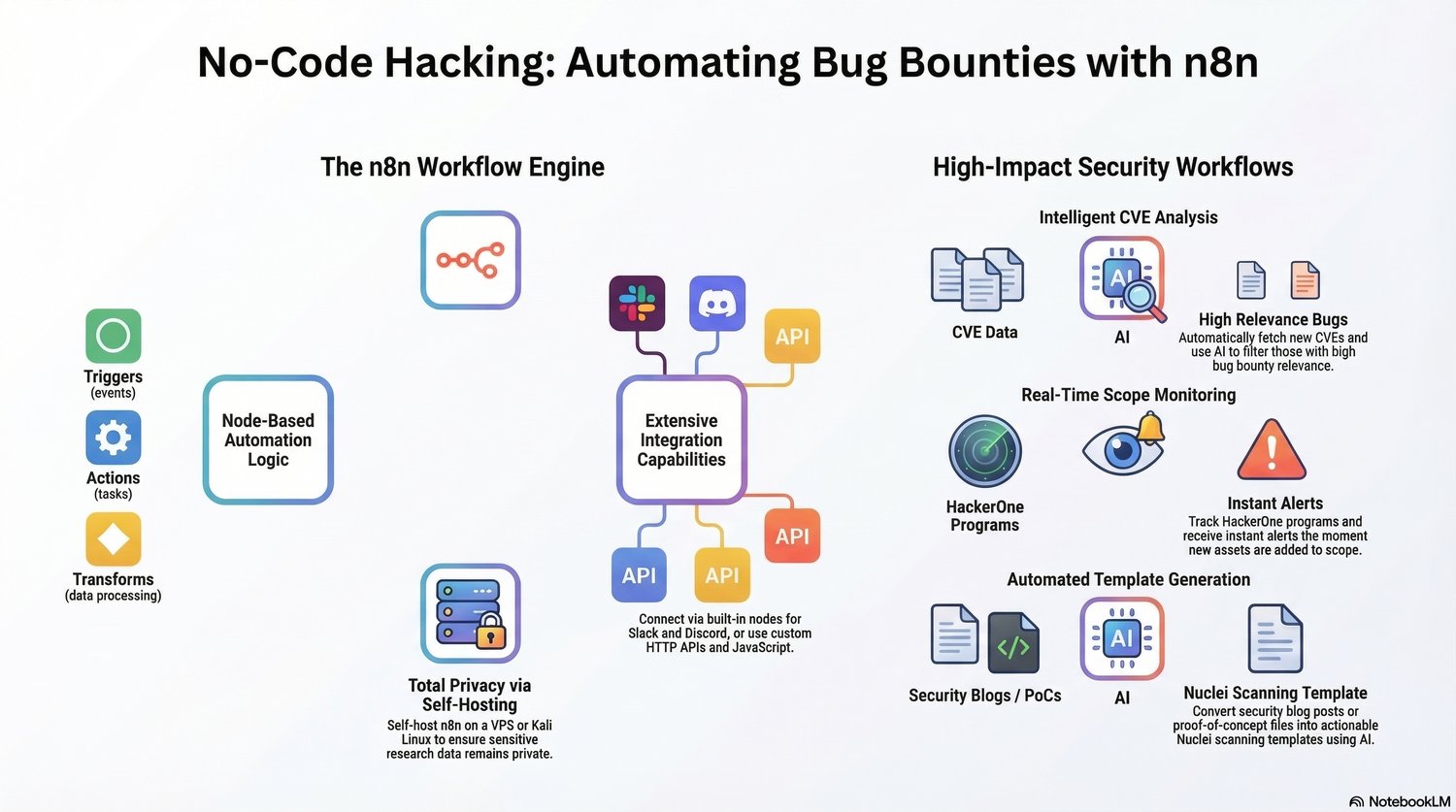
✔ How the n8n workflow engine powers automation with triggers, actions, and transformations
✔ How to connect APIs, Slack, Discord, and security tools into one workflow
✔ Building AI-powered CVE analysis pipelines to identify relevant vulnerabilities
✔ Real-time monitoring of bug bounty program scope changes
✔ Automated alerts for new HackerOne assets
✔ Using AI to generate Nuclei scanning templates from security blogs and PoCs
✔ Creating automated research pipelines for vulnerability discovery
✔ Self-hosting n8n on a VPS for privacy and full control
This guide is perfect for:
• Bug bounty hunters who want faster recon workflows
• Ethical hackers building automation pipelines
• Security researchers tracking vulnerabilities
• Cybersecurity students learning modern automation techniques
• Developers interested in security tooling
By using these techniques, you can save hours of manual work, track vulnerabilities faster, and improve your bug bounty efficiency.
Turn security research into intelligent automation.