👁️Recon Database (🐜Bug Bounty Series)
Most hunters don't lose bugs because they lack skill. They lose them because they lose track.
The Recon Database is the intelligence layer of Bug Bounty OS — a purpose-built Notion workspace that captures everything you discover about a target before you fire a single request.
No more scattered text files. No more retesting surfaces you already covered three weeks ago. No more missing the subdomain that was sitting there the whole time.
🔍 What's inside:
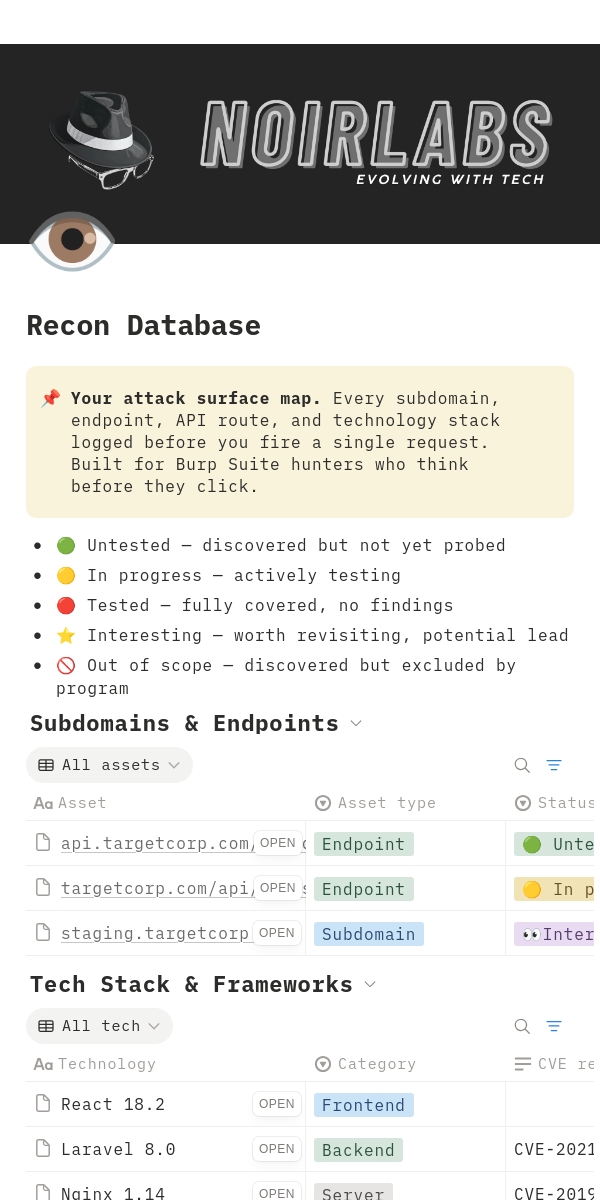
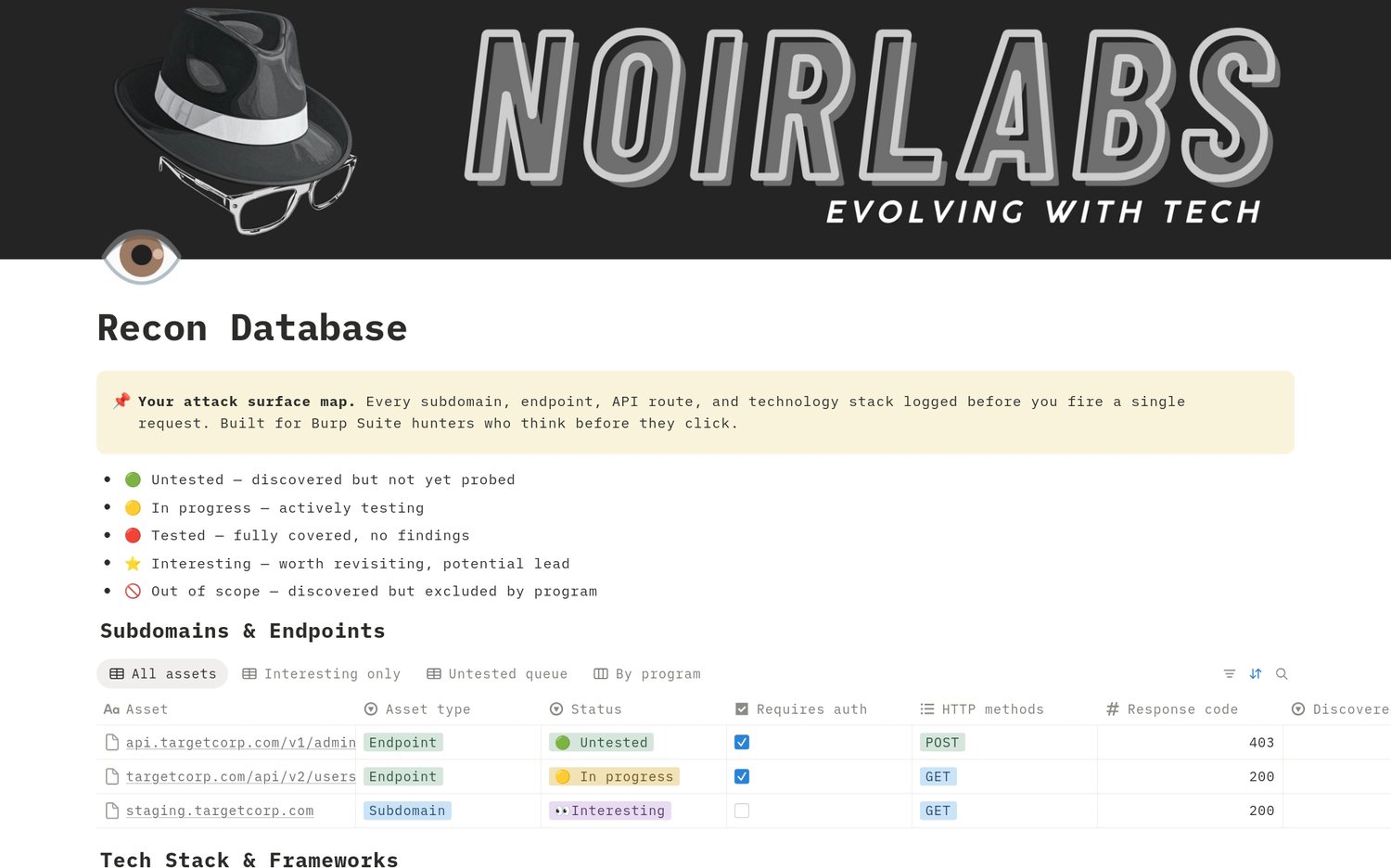
Subdomains & Endpoints — your master asset list. Every surface the target exposes, tracked by status, response code, auth requirement, and Burp observations. The Untested Queue view becomes your daily attack list.
Tech Stack & Frameworks — your vulnerability intelligence layer. Every technology identified, version logged, CVEs flagged. One view shows you exactly which installs are running known vulnerable versions — your highest value targets, surfaced instantly.
API Routes & Parameters — your deepest recon layer. Individual routes, HTTP methods, interesting parameters, and potential vulnerability types all mapped before you open Burp Intruder. The Potential Vulns view tells you where to focus.
⚡ Built around the Burp Suite workflow:
As you proxy traffic, log endpoints directly from the sitemap. Spot a framework version in a response header? It goes straight to Tech Stack with CVE references noted. Find a parameter worth fuzzing? Flag it in API Routes before you even open Intruder.
Everything links back to your Program Tracker and forward to your Findings Pipeline — so your recon feeds directly into your findings without retyping a single thing.