RHEA Crypt v5.2.2
Now $10!
Sale on this product as a new release is coming 03/21/2026.
Foundational - Ground Breaking New Computational Method Software
First and ONLY of its kind.
Based on Architecture DARPA themselves are working on.
RHEA Crypt v5.2.2 FoundersEdition Demo Video
📦 RHEA_Crypt — README PACK
Version: v5.2.2 — Sovereign Edition
Author: Paul M. Roe (EnigmaticGlitch)
Patent Reference: U.S. Provisional Patent #63/796,404
© 2025 — All Rights Reserved
🔹 1. Welcome to RHEA_Crypt (Sovereign Edition)
RHEA_Crypt is a hardened cognitive encryption engine that fuses chaotic Lorenz entropy, symbolic glyph modulation, and hardware-bound trust validation into a single executable.
It operates beyond classical cryptographic expectations, featuring:
Core Traits Description Chaotic Entropy
Lorenz Attractor–driven key cycles Glyph Epochs Symbolic modulation within encryption rounds
Trust Validation Recursive integrity checks and reseal events License Security
Machine-bound + shard-masked RSA signatures AES Layer Hardened AES-256-GCM encryption
GPU Support CUDA/MPS acceleration when available
Platform Windows x86-64 — self-contained EXE (Nuitka Hardened)
RHEA_Crypt does not negotiate security.
It generates it — with velocity.
🔹 2. Installation
Requirement Details OS
Windows 10 or later Architecturex86-64
Dependencies None — all embedded at compile
GPU (Optional) CUDA / MPS — detected automatically
Simply place the executable anywhere on your system.
No installers, no telemetry, no silent background behavior.
🔹 3. Activation Instructions
Step 1 — Generate Machine Hash
Run:
customer_hash.exe
This produces:
customer_machine_hash.txt
Send this file to your software provider.
(TecKnows Inc. / EnigmaticGlitch / Paul M. Roe @ tecknows.maine@gmail.com)
Step 2 — Receive Your License
You will receive:
/license/
product.lic
Place it in the same directory as the executable:
RHEA_Crypt-Sovereign_vX.exe
license/
product.lic
Do NOT rename the folder.
Do NOT embed it in subdirectories or inside the EXE.
Step 3 — Launch the Software
If valid → boots instantly.
If invalid → one of the following will be displayed:
Failure Code Meaning
❌ License Missing license/ folder not found
❌ Machine Hash Mismatch license tied to different machine
❌ License Expired renewal required
❌ License Signature Invalid license file tampered
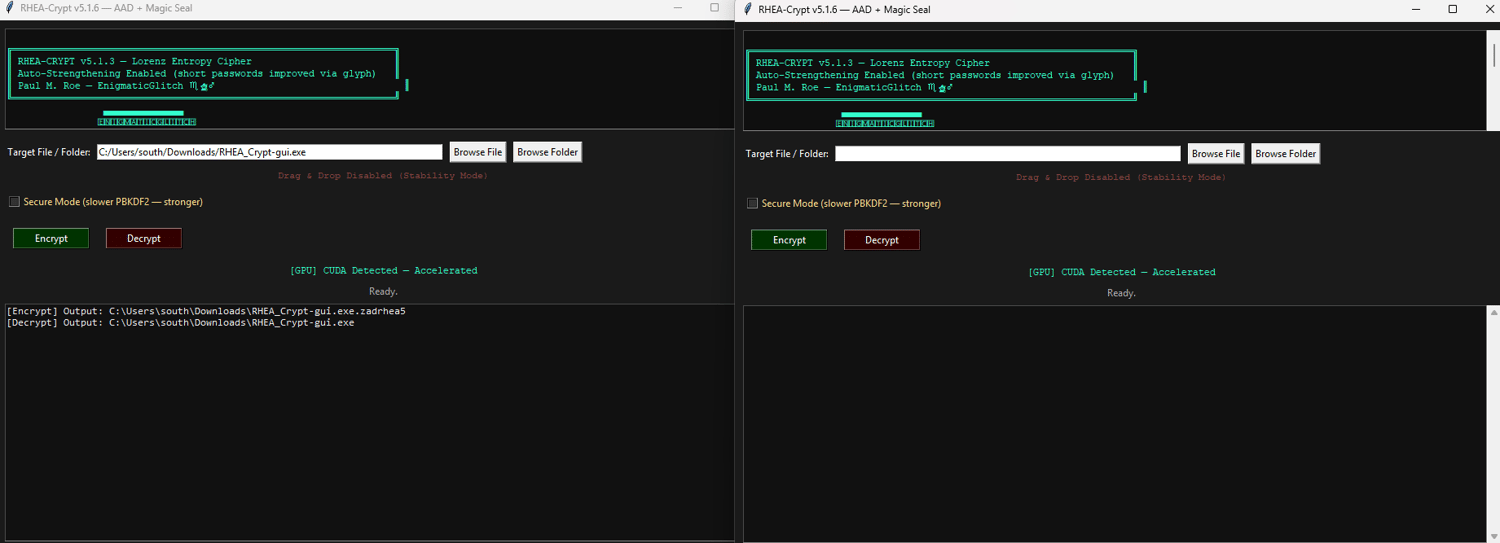
🔹 4. Usage Overview
- Select a file or directory
- Choose Encrypt or Decrypt
- Enter any passphrase
- (glyph-entropy modulation strengthens weak choices)
- Output appears next to the source
Encrypted output format:
*.zadrhea5
🔹 5. Security Model (Core Summary)
Layer Purpose
AES-256-GCM-Primary encryption
Lorenz Epochs-Chaotic entropy for key derivation
Recursive HMAC Salt-Passphrase strengthening
Symbolic / Glyphic Modulation-Trust shaped encryption noise
RSA-3072 Signatures-License validation
Sharded PK Reconstruction-Anti-tamper mechanism
Hardware Binding-Locked to physical machine
Nuitka Hardening-Obfuscated compiled build
🔹 6. Support
When requesting support, include:
- Machine Hash (from customer_hash.exe)
- RHEA_Crypt Version
- Error Description
- File Type (directory / file)
- Encrypt or Decrypt?
- GPU or CPU Mode (shown in GUI)
📧 Support Email: Provided at purchase
🧾 Refund Policy: No Refunds (see below)
📜 Terms of Use — Customer Agreement
RHEA_Crypt – Sovereign Edition
© 2025 Paul M. Roe — EnigmaticGlitch
Protected by U.S. Copyright Law (Title 17), DMCA,
and U.S. Patent Law (Provisional #63/796,404)
1. Grant of License
You receive a revocable, non-transferable, machine-bound license.
2. Permitted Use
You may:
- Run the software on the licensed machine
- Encrypt/decrypt your own files
- Use RHEA_Crypt for personal, professional, academic, or research workflows
3. Prohibited Use
You may NOT:
- Attempt to bypass or disable licensing system
- Reverse engineer, debug, or modify executable
- Resell or sublicense RHEA_Crypt
- Use it for illegal activity or concealment of crimes
- Train AI/ML systems on any part of the software or glyph infrastructure
4. Machine Binding
If multiple hardware components change, a new license may be required.
5. Updates
Updates may add:
- Enhanced encryption
- Performance improvements
- GPU features
- New licensing tiers (Sovereign, Ultra, Core)
Updates may require a new license.
6. Liability
The author is not liable for:
- Data loss or corruption
- Improper usage
- Hardware/GPU instability
- Lost passphrases
Software is provided as-is.
7. Governing Law
This agreement is governed by:
- U.S. Federal Law
- Maine State Law
- U.S. Patent & Copyright Statutes
- Sovereign Order of Enigmatic Republics
🛡 RHEA_Crypt — Software License Agreement (SLA)
1. Ownership
All components — engine, entropy logic, documentation —
are fully owned by:
Paul M. Roe (EnigmaticGlitch)
TecKnows, Inc. — Androscoggin County, Maine
All rights reserved.
2. License Structure
Feature Method Binding
Hardware-locked ValidationRSA-3072 authentication CyclesAES-256-GCM + Lorenz entropic keys
Obfuscation
Nuitka / XOR masking / anti-debug Glyph Sharding Symbolic masking + reseal
3. User Responsibilities
You agree to:
- Protect your passphrases
- Retain control of your machine
- Avoid distribution or exposure of your license
- Contact support if hardware changes occur
4. Anti-Tampering
Detection triggers instant license termination.
Unauthorized activity includes:
- Reverse engineering or debugging
- Bypassing licensing logic
- External code injection
- Key extraction attempts
5. Termination
License may be revoked if:
- Piracy is detected
- Misuse is confirmed
- Chargeback/refund dispute is filed
- Licensing is bypassed in any form
All rights cease immediately upon termination.
🚫 Refund & Customer Support Policy — NO REFUNDS
Due to the nature of encryption and digital licensing:
All sales are final. No refunds will be granted.
This includes:
- Incorrect machine hash
- Lost passwords
- System failure
- Changed mind
- Incompatibility issues
- “I didn’t understand what this is”
Once a license is generated, it cannot be rescinded or reassigned.
Replacement License Policy (Hardware Failure)
Scenario Outcome
Up to 4 hardware changes Existing license remains valid>4 component changes
New machine hash required Re-issue licenseAt creator’s discretion (may incur fee)
Support Covers
✔ License issues
✔ Activation problems
✔ General functionality questions
Support Does Not Cover
❌ Data recovery
❌ Password recovery
❌ File decryption without passphrase
❌ System repair