The Sovereign Custody Protocol™: A Systemic Exit Strategy
You own a brokerage account. But do you own what's inside it?
Since the 1994 revisions to UCC Article 8, the answer is legally — no.
When you hold wealth through a broker or custodian, you were quietly reclassified. Not an Owner with a property right. A Security Entitlement Holder with a contractual claim against an institution's ledger.
In a stable market, this distinction is invisible.
In a systemic liquidity event — when the $700 trillion derivatives complex faces a margin call — it becomes everything.
The mechanism already exists in the legal architecture. It is called the Collateral Sweep. Your brokerage account is legally available to satisfy the Super-Priority claims of the largest counterparties first. You are at the back of that line. What remains after the sweep is yours.
The Sovereign Custody Protocol™ is the operational blueprint for stepping outside this architecture entirely — before the mechanism triggers.
THIS IS NOT AN INVESTMENT PRODUCT.
It is not a trading course. It is not a newsletter. It is not a list of "safe assets" to buy.
It is an Architectural Blueprint for Asset Survivability — a systematic protocol for removing your wealth from the institutional collateral pool and installing it into a custody structure you control directly, with zero counterparty exposure.
Actionable high-density intelligence map. Three printable operational protocols. One complete system.
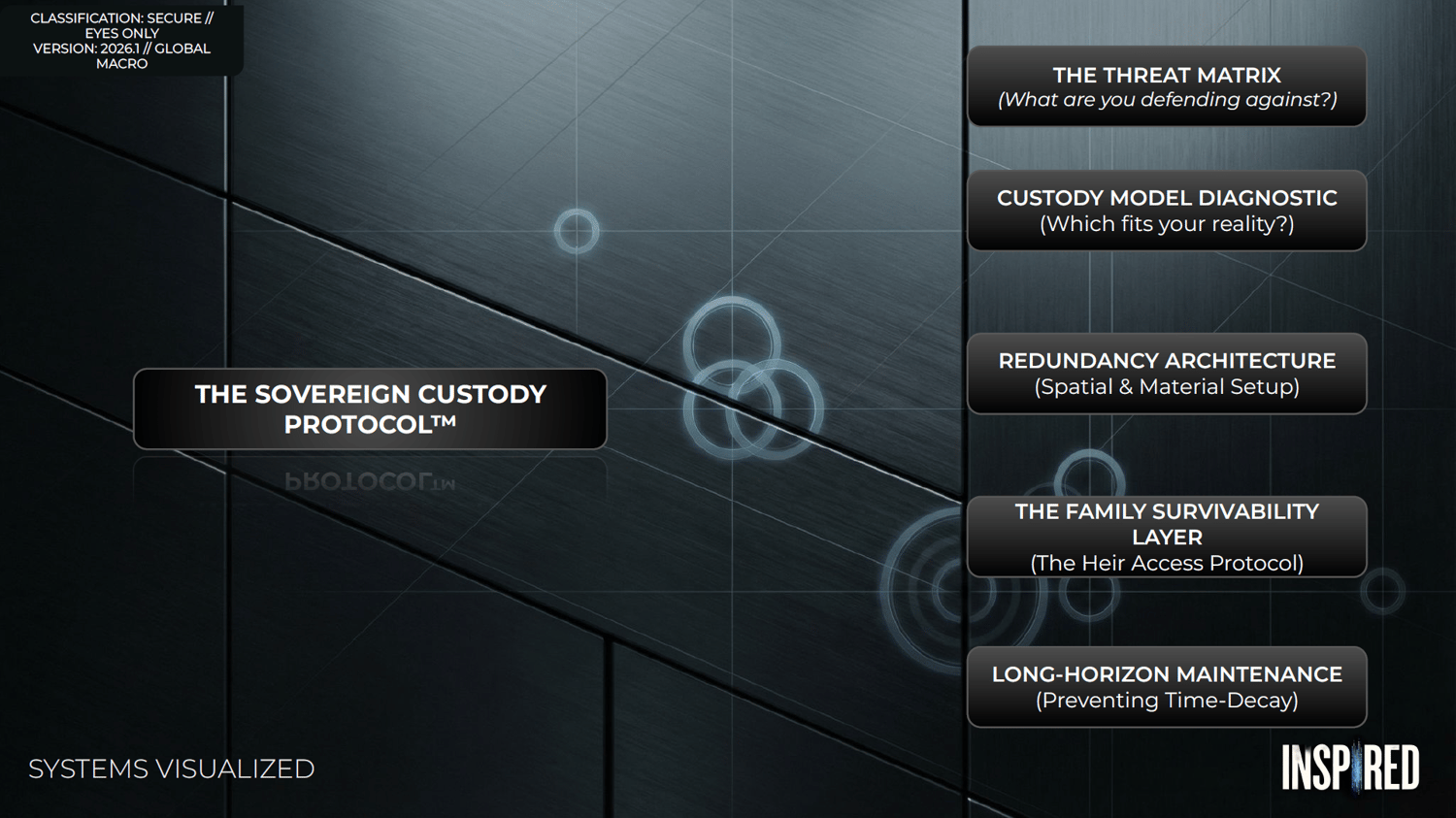
WHAT'S INSIDE THE PROTOCOL:
THE THREAT MATRIX Most custody guides tell you what to protect against. This one maps the full architecture of how wealth is actually lost — across three distinct vectors: Counterparty Risk (the institutional sweep), Physical Coercion (the threats most people never plan for), and Cognitive/Systemic Error (the self-inflicted failures that destroy more wealth than any market crash). You cannot build a defense against threats you haven't mapped.
THE CUSTODY DIAGNOSTIC A master decision matrix that matches your current wealth tier — from Solo Architect to Institutional — to the precise custody model your situation actually requires. Single-Sig, Multisig, or Collaborative Custody each have specific thresholds where they become the right answer and specific points where they become a liability. This module eliminates the most expensive mistake in self-custody: using the wrong architecture for your threat profile.
THE REDUNDANCY ARCHITECTURE One vault is not a system. It is a single point of failure with a combination lock on it. This module maps the spatial separation strategy used by family offices — the specific ring logic for distributing physical backups across jurisdictions, storage types, and access protocols so that no single event can eliminate your recovery options. The math of redundancy is not intuitive. This map makes it visual.
THE HEIR ACCESS PROTOCOL The most ignored failure point in sovereign wealth architecture. You can build the most technically secure custody system in existence — and leave your family with nothing if you haven't solved the cryptographic handoff problem. This module contains the complete Inheritance Handoff Template: a turnkey, plain-language document that allows a non-technical spouse or heir to access and recover your assets without you present. Built for the person who has never heard of a seed phrase. Designed to survive you.
LONG-HORIZON MAINTENANCE Cryptographic principles are permanent. The hardware that executes them is not. The signing device you buy today may be discontinued, incompatible, or physically degraded by 2036. This module delivers the maintenance cycle used by institutional custody operations — the annual audit protocol, the hardware replacement triggers, and the software migration checklist that ensures your fortress doesn't silently become a trap over the decade you're not watching it.
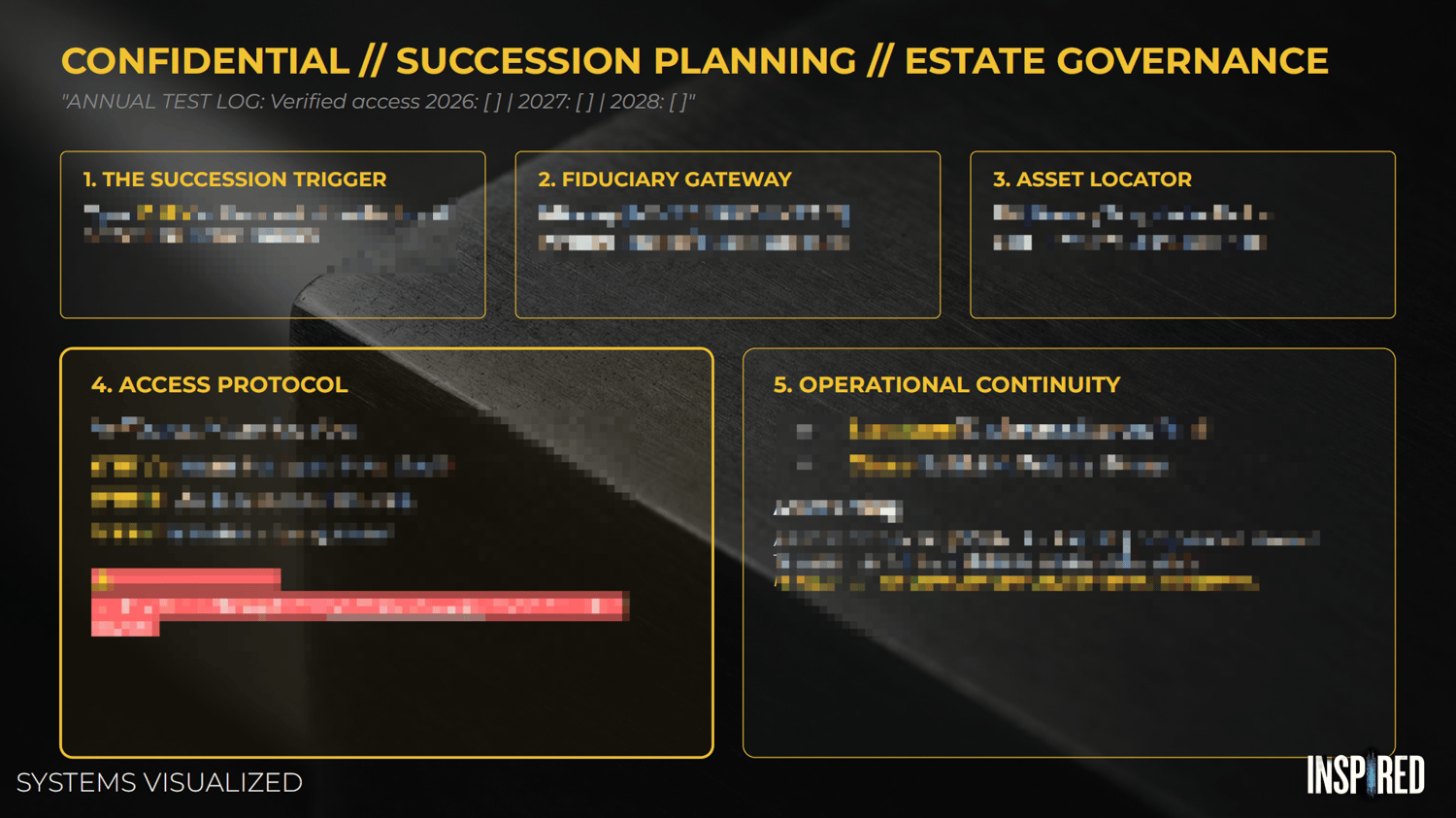
THE THREE PRINTABLE PROTOCOLS
Included with the blueprint — three operational documents designed to be printed, completed, and stored with your physical custody architecture:
→ The Custody Model Protocol — Your personal decision record for which architecture you've chosen and why, with the threshold triggers that would require you to upgrade it.
→ The Annual Sovereign Audit — A step-by-step maintenance checklist to run once per year. The exact process for verifying your hardware, testing your backups, confirming your redundancy chain, and updating your heir access documents.
→ The Succession Planning Template — The complete handoff document. Plain language. Zero technical prerequisites. The document your family follows if you are gone, incapacitated, or simply unavailable.
ON THE PRICE
This protocol is priced at $149.
The Architects who manage generational wealth spend tens of thousands annually on custody architecture, legal structures, and institutional-grade security protocols.
This is the distilled operational intelligence from that infrastructure — mapped into a visual system that a single individual can implement, maintain, and hand off without an army of advisors.
The question is not whether $149 is expensive.
The question is what the architecture protecting your wealth is currently worth — and whether you've actually built one.
THE ANALYST'S MANDATE
A fortress left unmaintained is just a trap for the next invader.
A chain of promises is just a liability with a logo on it.
The legal plumbing of the financial system is being rewritten right now — CBDCs, Basel III collateral frameworks, the UCC Article 8 architecture that reclassified you without a vote.
The Architects have already positioned outside it.
The Sovereign Custody Protocol™ is your map to the same exit.
Own your assets. Lock the gate. Stay Sovereign.
→ GET INSTANT ACCESS — $149