Metasploit API Guide
Deep dive into MSF internals
This isn’t just another resource on how to write modules — the Msf API Development Guide is a definitive blueprint for weaponizing the Metasploit Framework at a professional R&D level. You will gain the ability to engineer custom exploits, build sophisticated evasion layers that bypass top-tier security products, and orchestrate complex attack chain. It is the bridge between being a user and being an architect of offensive technology.
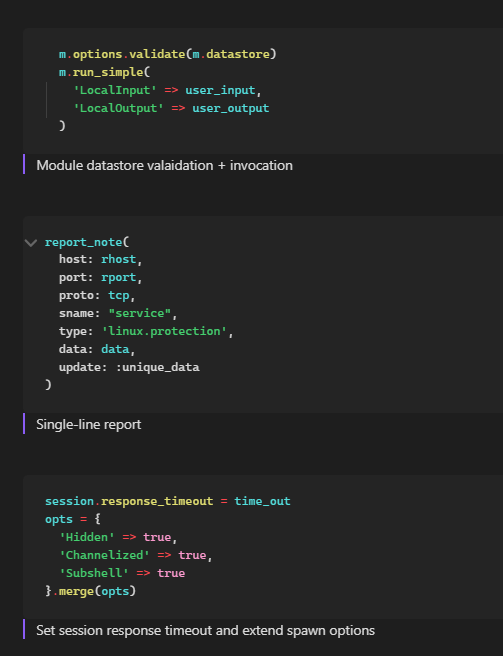
Beyond the strategic methodology, this package includes a set of meticulously formatted, high-density documentation covering the most critical APIs and mixins required for advanced framework extension. These observations are forged from years of long-term tool usage and real-world deployment, revealing subtle nuances in process migration, session persistence, and environment manipulation that are often overlooked. This knowledge provides the context necessary to turn raw code into a reliable and tested offensive asset, suited to run across various live targets.
- Architectural Domination: Master the internal libraries that govern how the framework interacts with system resources, allowing you to manipulate environment variables and system hives without leaving traditional footprints.
- Advanced Network Evasion: Learn to weaponize the framework’s low-level socket handling. By disabling standard delays and forcing custom TCP behaviors, you can bypass traffic analysis and behavioral triggers that flag default traffic of the framework.
- Invisible Post-Exploitation: Move beyond basic commands with advanced session management and pivoting. Learn to automate the filtering of active check-ins, weaponize the framework’s low-level socket handling and perform reconaissance/management with drastically reduced telemetry and IOC leftover.
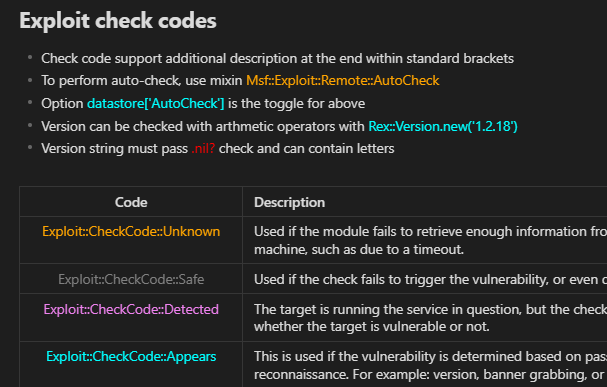
- The "Undocumented" Advantage: Access a comprehensive technical reference for host normalization, platform retrieval via encrypted channels, and the conversion of complex binary BOFdata into executable sequences.
This resource is designed specifically for Red Team Operators, Malware Engineers, and Exploit Developers
Format: PDF Reference / Guide Delivery: Instant access to a DRM-protected document.