CYBERPULSE AI RedOps: Role-Based LinkedIn Profile Discovery with Google OSINT
📝 Description:
Automates public profile discovery for CISO, CEO, and other key roles using Google Programmable Search. Extracts LinkedIn profile links, names, and timestamps to a structured Google Sheet for OSINT, exposure analysis, or Red Team prep.
✅ Who’s It For:
- Red Teams planning phishing simulations
- OSINT investigators and social engineers
- Cybersecurity trainers mapping exposure risk
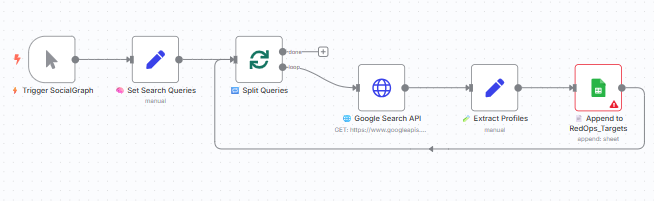
⚙️ How It Works:
- Triggers manually or on schedule
- Loads role-based search queries (e.g. "CISO site:linkedin.com")
- Queries Google Custom Search API
- Parses and extracts names and profile links
- Logs findings to Google Sheets for review
📦 Requirements:
- Google Programmable Search Engine (API key + CX ID)
- Google Sheets credentials
- Optional: Search query editing
📁 File Templates:
- RedOps_SocialGraph_Log_Template.xlsx
namelinkedinteamstatusmoduletimestampJohn Doehttps://linkedin.com/in/johndoeGRCactiveSocial_Graph_Builder2025-07-27T12:00:00Z
🧠 Customization Tips:
- Update queries (CISO, CEO, VP IT, etc.)
- Filter results by region or org using site filters
- Extend to track Twitter or GitHub links
⚖️ Ethics Note:
This tool uses public Google Search results. It is meant for educational or internal red teaming only. Do not use for scraping or unauthorized targeting.
🔗 Part of the CYBERPULSE AI RedOps Suite